Someone on the dark web is apparently trying to sell a Windows zero-day exploit for $220,000. The flaw targets Remote Desktop Services and could let attackers completely take over vulnerable machines.
According to a post spotted by X user Dark Web Informer, a hacker using the alias Kamirmassabi advertised the exploit on an underground forum, describing it as a Windows zero-day that enables privilege escalation on Windows 10 and Windows 11. The $220,000 price tag suggests it is likely aimed at well-funded state-backed groups or corporate espionage operations rather than typical cybercriminals.
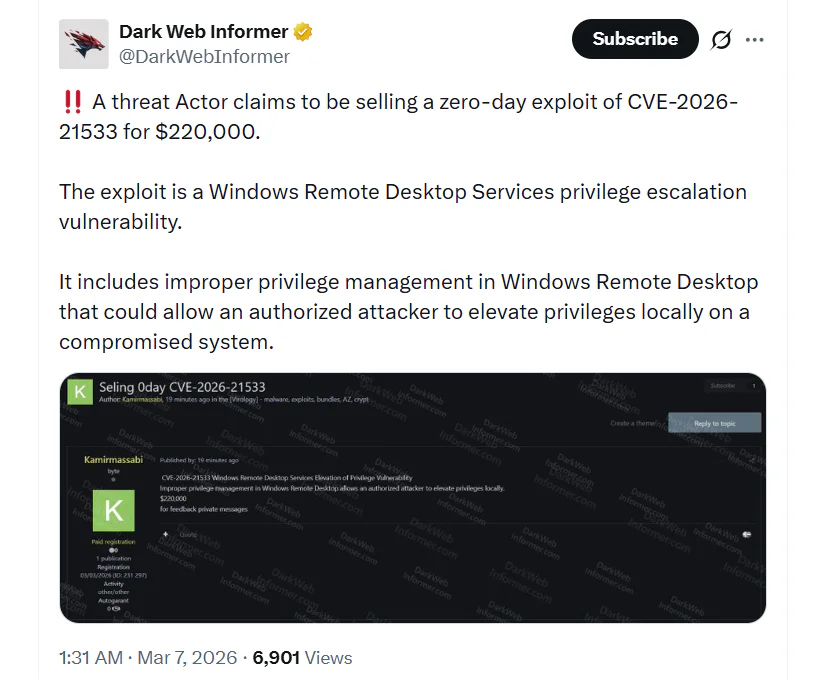
The flaw, tracked as CVE-2026-21533, is linked to improper privilege handling within Windows. It allows an attacker who has already gained access to a machine to elevate their permissions to the highest system level. With that access, they could run arbitrary code, install software, modify registry entries, steal sensitive data, and change system configurations without limitation.
The vulnerability is rated as remotely exploitable and affects a wide range of Microsoft products, including Windows 10, Windows 11, and all Windows Server versions from 2012 to 2025. It has been given a CVSSv3 score of 7.8, indicating high severity.
The exploit requires the attacker to already have limited access to the target device. How that initial access is achieved is still uncertain, although some experts believe phishing campaigns that persuade users to download malicious files may play a role.
Microsoft has confirmed that the vulnerability has already been exploited in real-world attacks, although the company did not share details about specific incidents. The tech giant said the issue was fixed in its February Patch Tuesday release, meaning systems that have installed the latest updates are no longer exposed to this attack path.
In cases where enterprise systems cannot be patched immediately due to operational or compliance policies, administrators are encouraged to adopt temporary safeguards. These include disabling Remote Desktop Services if it is not necessary, restricting access to trusted networks, and following CISA BOD 22-01 guidance for managing known exploited vulnerabilities. Endpoint Detection and Response solutions may also help identify suspicious registry activity or privilege escalation attempts.
At the same time, another critical Windows vulnerability has caught the attention of security experts. The flaw, tracked as CVE-2026-2636, affects the Windows Common Log File System driver and can be exploited to cause a denial-of-service crash. It was identified by Ricardo Narvaja of Fortra, and attackers with basic privileges can trigger a Blue Screen of Death. A proof-of-concept exploit has already been released.
Maybe you would like other interesting articles?

