The Linux ecosystem is dealing with another critical privilege-escalation vulnerability shortly after a previous high-severity issue required rapid attention from administrators. The “Dirty Frag” bug is reported to have been present in the kernel for nearly nine years, allowing local attackers to gain root access and impacting most major distributions.
Security researcher Hyunwoo Kim, known online as V4bel, published details of the “Dirty Frag” vulnerability after a third party released a working proof-of-concept exploit ahead of schedule, forcing an early disclosure more than a month before Kim’s planned announcement. No patch has been released so far, and the issue is being tracked under two related CVEs: CVE-2026-43284, linked to an xfrm-ESP page-cache write issue, and CVE-2026-43500, tied to an RxRPC page-cache write flaw.
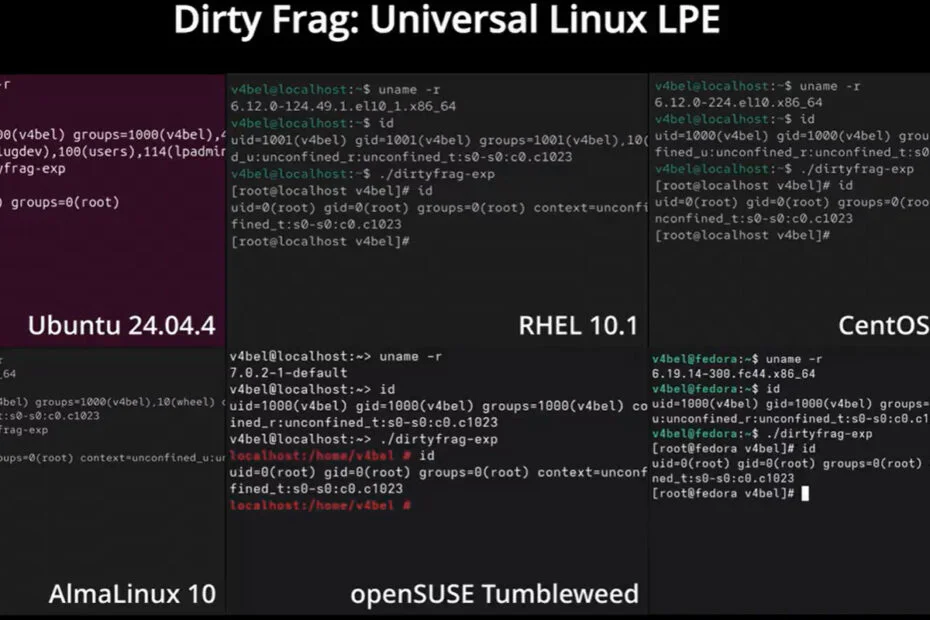
Dirty Frag basically links those two bugs together into what Kim calls a kind of universal local privilege-escalation exploit. It’s in the same family as Dirty Pipe and the newer Copy Fail issue that popped up just a couple of weeks ago. The interesting part is that it’s not random or unstable; it’s predictable, doesn’t crash the system, and has worked pretty reliably in tests on Ubuntu, RHEL, Fedora, openSUSE Tumbleweed, CentOS Stream, and AlmaLinux.
The root cause traces back to code added to the Linux kernel in 2017. Because the vulnerable components exist in most modern distributions, the scope of impact is broad, even though identification of all affected kernel versions is still ongoing. Kim’s technical write-up also states that mitigations for Copy Fail do not address Dirty Frag, as the two issues are independent.
The only available mitigation at this stage is the removal of vulnerable kernel modules. Administrators can unload esp4, esp6, and rxrpc via a single command, effectively neutralising the exploit chain. This comes at a cost, however, as it disables IPsec-based VPN functionality and the AFS distributed file system. Organisations relying on either capability must weigh exposure risk against operational disruption until a formal patch is released.
The early disclosure has frustrated parts of the kernel development community that had been working privately with Kim on preparing patches. It has also renewed interest in a proposal among maintainers for a kill-switch mechanism that would allow system administrators to disable specific kernel functions under active exploitation. The aim is to reduce the window of vulnerability while permanent fixes are developed and tested, allowing systems to remain operational in the meantime. With root-level vulnerabilities appearing at a pace described by some developers as concerning, the idea is gaining traction.
Maybe you would like other interesting articles?