Google has moved up its timeline to protect its infrastructure from quantum computing risks, targeting full readiness by 2029, well ahead of most industry and government plans. The move caught many cryptography experts off guard and signals the company believes “Q Day,” when quantum systems could crack today’s encryption, may arrive sooner than expected.
Google shared the news in a blog post, explaining how it plans to move to post-quantum cryptography (PQC), algorithms designed to hold up against quantum computer attacks.
“As a pioneer in both quantum computing and PQC, it’s our responsibility to lead by example and share an ambitious timeline,” wrote Heather Adkins, Google’s vice president of security engineering, and Sophie Schmieg, a senior cryptography engineer. “By doing this, we hope to provide the clarity and urgency needed to accelerate digital transitions not only for Google, but across the industry.”
Until now, most organizations had relied on milestones set by the U.S. government and defense agencies, which generally target 2030 to 2033 for full quantum readiness.
“That is certainly a significant acceleration/tightening of the public transition timelines we’ve seen to date, and is accelerated over even what we’ve seen the U.S. government ask for,” said Brian LaMacchia, a cryptography engineer who led Microsoft’s post-quantum transition between 2015 and 2022 and now works at Farcaster Consulting Group, in an interview with Ars Technica. “The 2029 timeline is an aggressive speedup but raises the question of what’s motivating them.”
Google did not explain why it set an earlier deadline. Still, the company’s research has repeatedly pushed forward estimates for when quantum attacks could begin undermining today’s cryptographic systems.
Last year, Google researchers led by Craig Gidney reported that a quantum computer with one million noisy qubits could crack a 2,048-bit RSA key in less than a week. The finding significantly lowered earlier assumptions; in 2019, estimates suggested the task would need around 20 million qubits.
Alongside the broader announcement, Google also shared its first detailed roadmap for making Android quantum-resistant. In a separate post, the company said it will introduce support for ML-DSA, a digital signature algorithm standardized by the National Institute of Standards and Technology, beginning with the Android 17 beta. The algorithm will be built into Android’s hardware root of trust, enabling developers to sign and verify apps using post-quantum cryptographic keys.
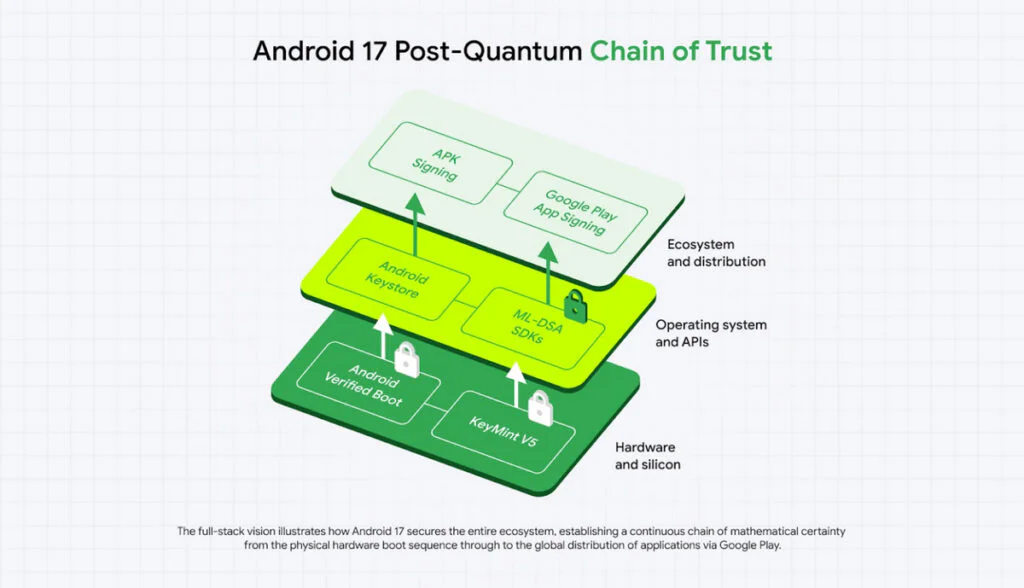
According to Google, ML-DSA has been integrated into the Android Verified Boot library to protect the operating system’s boot sequence from tampering. Engineers are also migrating Android’s remote attestation, which verifies device integrity to enterprise or cloud services, to post-quantum cryptography.
Future updates will bring ML-DSA support to the Android Keystore for secure on-device key generation, with plans to later expand the technology to the Google Play Store and its app-signing workflow.
The transition will require developers to revise signing, verification, and authentication workflows. Google said the work reflects what it views as a necessary shift to prioritize PQC migration for authentication services, a key part of strengthening online security and digital signature systems.
For cryptographers, Q Day has been a moving target for decades. Since mathematician Peter Shor revealed in the 1990s that a sufficiently powerful quantum computer could factor large integers exponentially faster than classical systems, the timeline for breaking RSA encryption has fluctuated, with the required quantum resources steadily decreasing over the years.
Although the timeline remains uncertain, cybersecurity planners are treating quantum risks as urgent. The National Security Agency aims to transition national security systems to post-quantum cryptography by 2033, with earlier milestones in 2030 and 2031. At the same time, companies such as Signal, Cloudflare, and Apple have begun integrating NIST-approved PQC algorithms, including CRYSTALS-Kyber and ML-KEM-768, often on a limited basis.
Maybe you would like other interesting articles?

